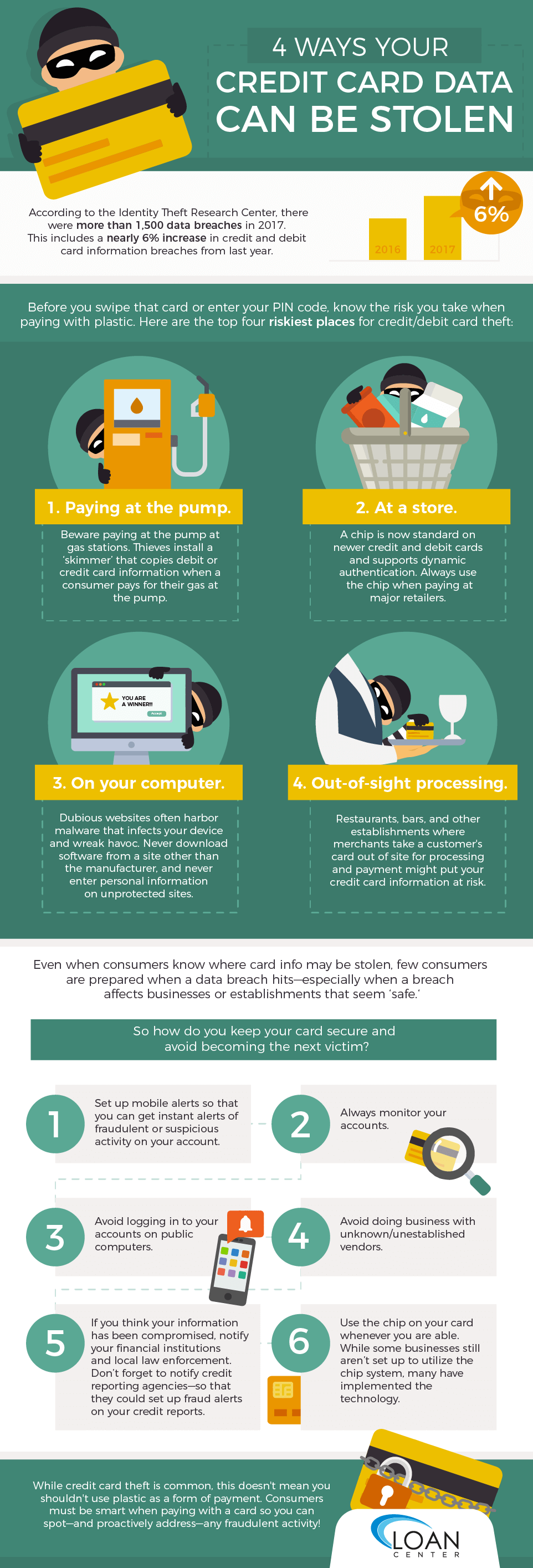
Paying with a credit card is convenient and saves most of us the time of ruffling through our cash and change at the register. But while that piece of plastic seamlessly secures payments without the hassle, those embossed numbers on your card are one of the most seductive pieces of financial information for identity thieves. According to the Identity Theft Research Center’s “2017 Annual Data Breach Year-End Review,” there were more than 1,500 data breaches in 2017 and “nearly 20 percent of breaches included credit and debit card information, a nearly 6 percent increase from last year.”
Although criminals still love to steal social security numbers for more elaborate identity theft schemes, credit or debit card information allows thieves to have quick access to cash and financial equity. While many consumers believe that financial theft is more likely to occur while shopping online when card information is entered via payment sites (secured or possibly unsecured), credit card theft can happen even in places where consumers least expect it.
Before you swipe that card or enter your PIN code, know the risk you take when paying with plastic. Here are the top four riskiest places for credit/debit card theft:
1. Paying at the pump.
Before the 4th of July holiday, the Secret Service issued a warning to all Americans traveling during the holiday season: Beware paying at the pump at gas stations. Thieves install a ‘skimmer’ that copies debit or credit card information when a consumer pays for their gas at the pump. Some skimmers are noticeable, and you may see that the pay slot at the pump was manipulated. However, other skimmers are internal and not clearly visible. A story by ABC affiliate 33/40 out of Birmingham, Ala. recommends using your phone’s bluetooth to check for a possible skimmer. Why? Your Bluetooth will show a list of numbers that are trying to connect, according to the station. So how prevalent are skimmers? An article on ABC News reported that the Secret Service already located and removed “59 skimmers at 85 locations.” Instead of swiping your card at the pump, pay inside at the register.
2. At a store.
Target made headlines when it was revealed that thieves breached their system and stole credit card numbers from shoppers. The breach was the result of a cyber attack that allowed hackers to gain access to Target’s info. According to an article on ZDnet, the attacks began sometime near Black Friday in 2013. The attack was a stealthy and intricate internet hack; ZDnet explains that the hackers gained access to Target’s system through a third-party vendor. A Trojan virus was planted with the vendor, and this allowed hackers to gain access to the vendor’s info and credentials. The rest of the scheme is a complicated web of hacker activity. Tens of millions of customers were affected by the breach, and banks and credit unions across the country had to cancel old cards and reissue new ones to help combat the financial firestorm. Target later settled with victims paying about $10 million total—or $10,000 per victim.
The hack illuminated the vulnerability of credit information–even at the largest of Big Box stores– and the massive breach possibly helped usher in the era of the more secure ‘chip’ technology. The ‘chip’ is now standard on many newer credit and debit cards, and, according to information from J.P. Morgan Chase, this technology differs from the magnetic strip of older cards in that it cannot be ‘skimmed’ and the chip technology “supports dynamic authentication.”
When shopping at major retailers, always ‘chip’ your payment! However there is a guaranteed that this won’t happen at a LoanCenter Store. Or you can apply right on your computer are smart phone, by applying for a online title loan. If are looking for a title loan in Los Angeles just stop by and say hi at our headquarter location!
3. On your computer.
Almost everyone has opened a webpage and suddenly bombarded with some weird error message or lots of pop-ups. Or perhaps a message illuminates on the screen proclaiming that your device was chosen for a major prize. Fraud alert! Dubious websites often harbor malware that infects your device and wreak havoc. Some of these viruses even log your keystrokes—tech savvy experts know this as a “Keylogger Trojan.” This virus allows hackers to see passwords and other valuable information that may even help them steal your identity or financial information.
Never download software from a site of a company you are not familiar with, and never ever enter personal information on unprotected sites. If you don’t see a lock next to the url of a site, then assume it is unprotected.
All computers and devices also should have updated antivirus software that is turned on! Scan your computer regularly to detect (and remove!) any nasty viruses or malware. So what exactly are you looking for when trying to detect a virus? The experts at Norton Antivirus posted some obvious signs that you might need to scan the computer ASAP:
- Lots of pop-up ads. There will be a flood of one ad popping up after another. They won’t stop!
- A frozen screen and a message from law enforcement. No, the police aren’t out for you. This is a hacker scheme that’s looking to get a ransom out of you. According to Norton, it’s a bad one.
- Emails from your friends asking why you’re sending them files or posting weird things on social media! Your email or social media account was likely hacked, and your contact list was targeted. Those files are viruses that have been distributed to your nearest and dearest.
- Your computer is slow or crashes. This can be a sign of a virus. Scan the system to double check. If your computer is old, though, this could just be age!
4. When your card is taken out of sight for processing.
Restaurants, bars and other establishments where merchants take a customer’s card out of sight may put card info at risk. Not all employees are ruthless or out to victimize consumers, but some may be thieves who steal your information. Cash is best for purchases where your card ventures out of sight. When you hand over your information blindly, you risk having that data stolen or ‘skimmed.’ Think twice before paying with plastic
Even when consumers know where card info may be stolen, few consumers are prepared when a data breach hits—especially when a breach affects businesses or establishments that seem ‘safe.’ Most consumers don’t always know how massive many breaches are until they make national news. The Identity Theft Research Center released a report titled 2017 Data Breach Stats that lists each company or agency where information was breached. The compilation is eye-opening and a must-read for consumers.
So how do you keep your card secure and avoid becoming the next victim?
- Set up mobile alerts so that you can get instant alerts of fraudulent or suspicious activity on your account.
- Always monitor your accounts.
- Avoid logging in to your accounts on public computers.
- Avoid doing business with unknown/unestablished vendors.
- If you think your information has been compromised, notify your financial institutions and local law enforcement. Don’t forget to notify one of the three major credit reporting agencies—Experian, Equifax and TransUnion—so that they could set up fraud alerts on your credit reports.
- Use the chip on your card whenever you are able. While some businesses still aren’t set up to utilize the chip system, many have implemented the technology.
When you’re online, you also must always pay attention to sites that require you to enter personal information. While, yes, the lock on a url will signal that the site is secure, you also can check the list of breaches provided by the Identity Theft Research Center to see if a certain site has been affected in the past.
Although most breaches happen online, at skimmers or at stores, thieves also can access your info the old-fashioned way—physical theft of your card. Almost everyone has left a wallet or purse behind, only to realize the missing item later. Most often, the item is returned. However, honesty isn’t always the norm. And when you realize that a debit or credit card is missing, you must take action. Your bank or financial institution can cancel the card, reissue a new one and notify you of any fraudulent charges. However, you must be aware of your financial institution’s policies regarding stolen information. Some charges might not be covered, although many banks and credit unions typically work with their clients in good faith. Be sure to read the fine print of your credit card agreement and be familiar with how to dispute fraudulent charges.
If your debit card has been stolen, you need to act as soon as possible. Unfortunately, as debit cards are linked directly to a bank account, the fraudulent charges will affect your financial bottom line immediately. One of the best ways to stay on top of your accounts is to check them regularly. Review charges linked to checking or other accounts so you can spot any sketchy charges or withdrawals. If your debit card has been compromised, here are the immediate steps you need to follow:
- Call the number on the back of your card (if you still physically have the card). This is the company who will deal with the theft; this may or might not be your bank. Often, it is a third-party affiliate.
- Report the fraudulent charges to the bank and/or to the third party affiliated with the card.
- Ask for the card to be cancelled immediately, and explain the situation. You will likely be transferred to another representative who can handle the theft.
- Change your PIN.
ConsumerFinance.gov recommends that you follow up with a letter to address the inquiry; be sure you save a copy of this letter for your own reference. You also should keep track of all phone calls and messages you leave with your bank or other providers. Also, the site notes that “if your physical credit card has not been lost or stolen, you’re not responsible for unauthorized charges.”
While credit card theft is common, this doesn’t mean you shouldn’t use plastic as a form of payment. Consumers must, however, be smart when paying with credit or debit cards. Don’t let the card out of your sight, refrain from paying at the pump, utilize chip technology and always monitor your credit and financial accounts so you can spot—and proactively address—any fraudulent activity.

